Windows LAPS (Local Administrator Password Solution) is now built directly into Windows and does not require installation of the legacy Microsoft LAPS. All modern features are available without referring back to the old solution, making deployment simpler and more secure. In this blog post, we’ll explore how to use Microsoft Intune together with Windows LAPS to automatically manage and rotate local administrator passwords across Windows 10 and Windows 11 devices. This step‑by‑step guide will help IT admins strengthen endpoint security, enforce password rotation policies, and streamline management of local admin accounts.
Windows LAPS is now built-in with the following OS version installed April 2023 Updates, or any later version.
- Windows 11 22H2
- Windows 11 21H2
- Windows 10
- Windows Server 2022
- Windows Server 2019
- Pre-requisites
- How to Manage Windows LAPS policies with Microsoft Intune
- How to Review policy assignments from the Intune console
- How to Retrieve Local Admin Password for a Device
- Review the Windows LAPS policy assignment status on a device
- How to rotate local admin password from the Intune console
- Conclusion
- Related Posts
Pre-requisites
Before configuring Windows Local Administrator Password Solution (Windows LAPS) with Intune, ensure the following requirements are met:
Operating System Support
- Windows 10 (version 20H2 or later, with April 2023 cumulative update that introduces native Windows LAPS support)
- Windows 11 (April 2023 update or later)
- Windows Server 2019/2022 (with latest cumulative updates for Intune LAPS integration)
Licensing & Intune Requirements
- Active Microsoft Intune subscription
- Azure AD Premium P1/P2 for role-based access control (RBAC) and conditional access
- Devices must be Azure AD joined, or Hybrid Azure AD joined, and enrolled in Intune
Permissions & Roles
- Intune Administrator or Security Administrator role to configure LAPS policies
- Optional: Helpdesk RBAC role for password retrieval without elevated rights
Connectivity & Updates
- Devices must have internet connectivity to sync with the Intune service
- Latest cumulative updates installed to ensure the Windows LAPS policy CSP is functional
- Verify Intune Management Extension is running properly for policy deployment
Security Baseline Alignment
- Password complexity and rotation interval are defined in the Intune LAPS policy
- Ensure compliance with organizational security baselines for local admin accounts
How to Manage Windows LAPS policies with Microsoft Intune
You can leverage Microsoft Intune Endpoint Security policies for account protection to configure and manage Windows LAPS on devices enrolled with Intune. This Intune LAPS setup enables secure local administrator password management and automated password rotation across Windows 10 and Windows 11 endpoints. By integrating LAPS Intune policies, organizations can simplify configuration, strengthen endpoint security, and ensure compliance with password rotation best practices.
Intune policies can:
- Enforce password requirements for local admin accounts
- Backup local admin account from the device to your Active Directory or Azure AD
- Schedule rotation of those account passwords to help keep them safe
- Enforce password requirements for local admin accounts
You can also view details about the managed local admin accounts in the Intune Admin center, and manually rotate their account passwords outside of a scheduled rotation. Let’s understand how to configure LAPS in Intune.
1. Role-based access control for Windows LAPS
The following permissions are required to manage LAPS policy.
Create and access LAPS policy: The Endpoint Security Manager built-in role includes necessary permissions to manage LAPS policy by default. For a custom role, your account must be assigned sufficient permissions from the Intune RBAC category for the security baseline.
Rotate local Administrator password: To use the Intune admin center to view or rotate a device’s local admin account password, your account must be assigned the following Intune permissions:
- Manage Device: Read
- Organization: Read
- Remote tasks: Rotate Local Admin Password
Retrieve local Administrator password: To view password details, your account must have one of the following Azure Active Directory permissions:
microsoft.directory/deviceLocalCredentials/password/readmicrosoft.directory/deviceLocalCredentials/standard/read
Related Post: How to Create Custom RBAC Role in Intune for LAPS Password Administrator
2 Enable Windows LAPS in Entra ID
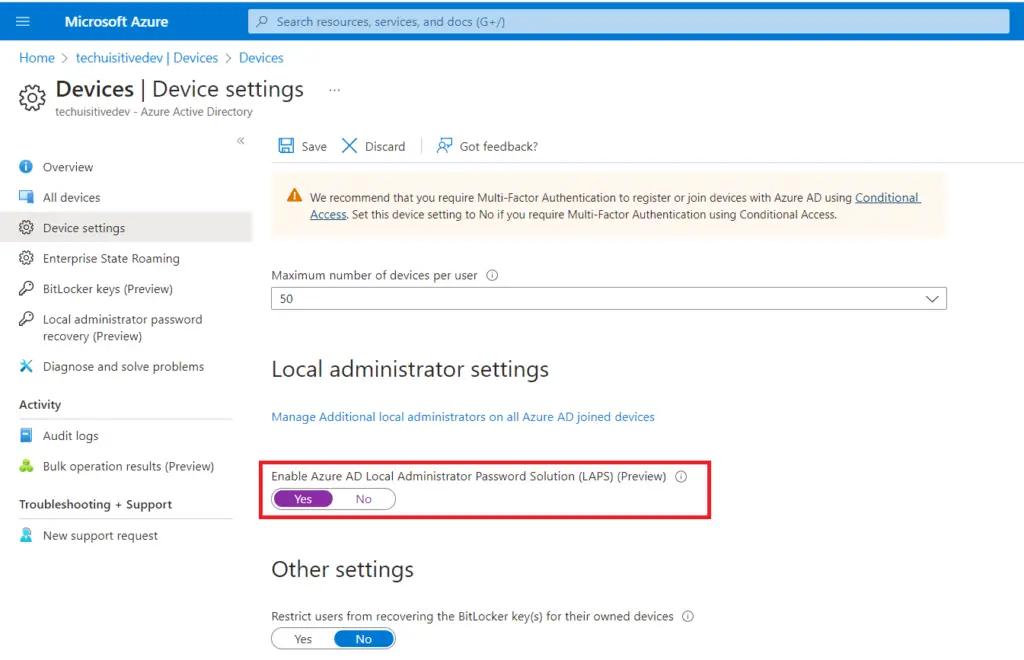
Before you start managing the local administrator password using Intune, the LAPS settings need to be enabled in Azure Active Directory. To enable the settings, go to Azure Active Directory > Device > Device Settings and turn on “Enable Azure AD Local Administrator Password Solution (LAPS) (Preview)“.
3. Create a policy in Microsoft Intune for LAPS setup
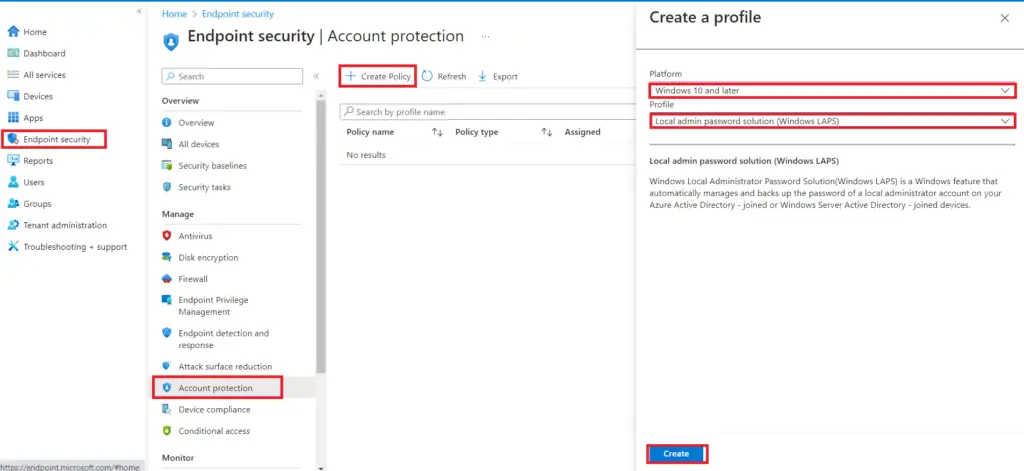
Step 1: To create a policy in Microsoft Intune, navigate to Endpoint Security / Account Protection, click on Create policy, and select the following
Platform: Windows 10 and later
Profile: Local admin password solutions (Windows LAPS)
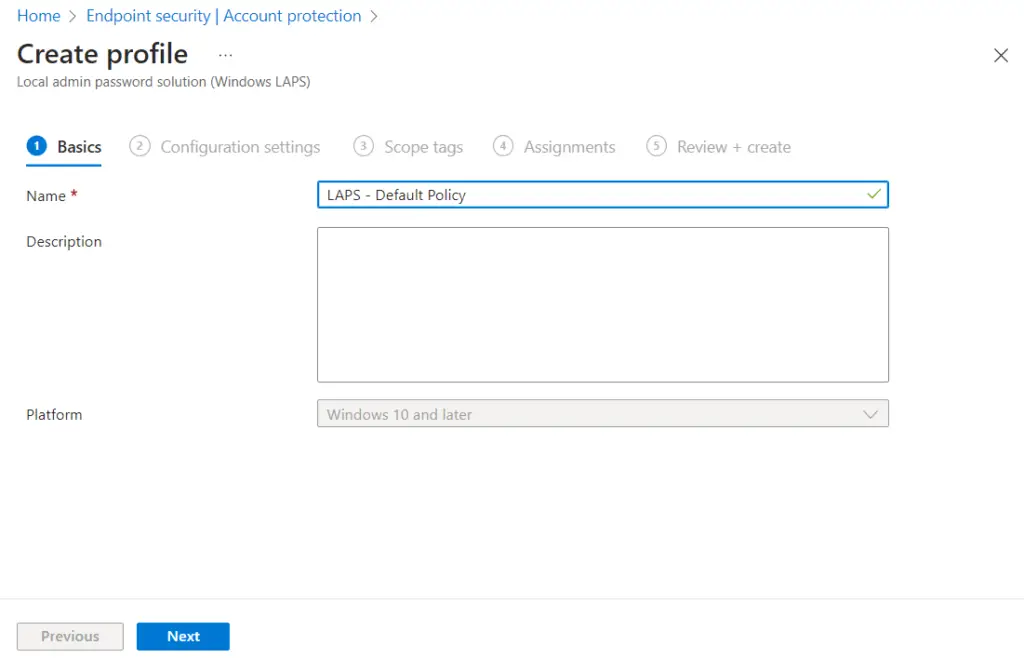
Step 2: Enter a policy name
Choose a clear, descriptive name such as “Windows LAPS – Local Admin Password Policy”.
This helps identify the profile later when managing multiple Intune LAPS configurations.
Optionally, add a description to document the purpose (e.g., “Configure Intune LAPS for automated password rotation on Windows 10/11 devices”).
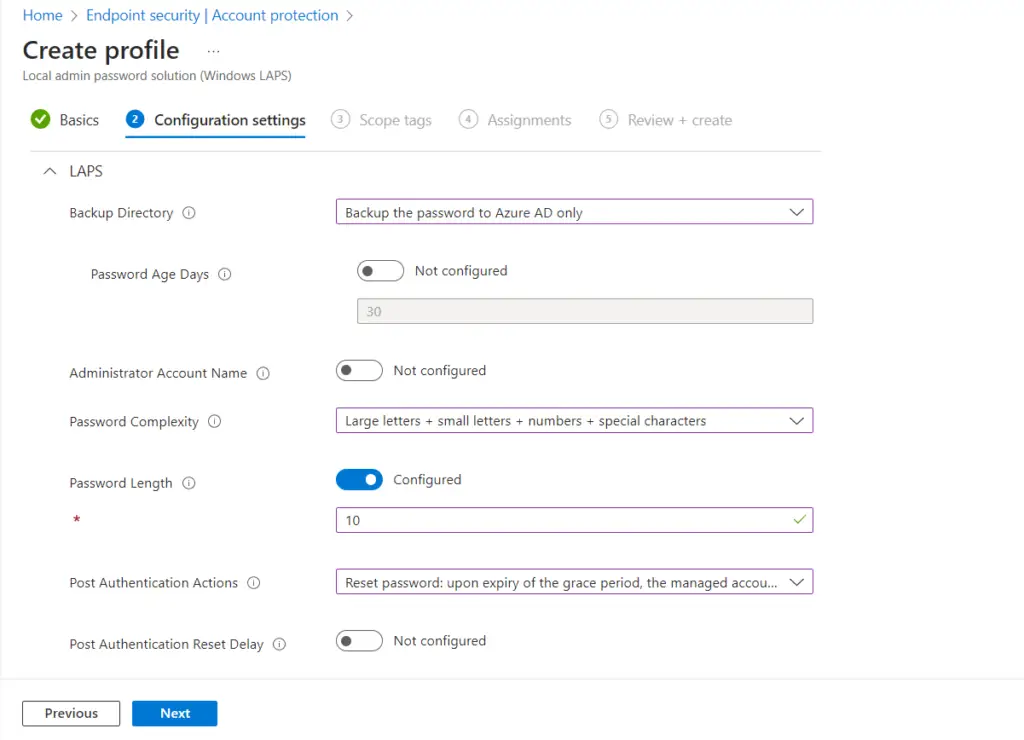
Step 3: On the Configuration Settings page in the Intune admin center, you define how Windows LAPS will manage local administrator passwords across enrolled devices. This is the core of your Intune LAPS setup:
Backup Directory
Define where the password is stored (Azure AD). The following options are available.
- Back up the password to Azure AD only
- Disabled (Password will not be backed up)
- Back up the password to Azure AD only
- Back up the password to Active Directory only
- Not Configured
Password Age Days
Set how frequently Intune LAPS rotates the local administrator password (e.g., every 30 days). Automated rotation ensures compliance with security baselines and eliminates stale credentials.
Administrator Account Name
Choose whether to manage the built‑in Administrator account or specify a custom local admin account. This ensures Intune LAPS policies apply consistently across all endpoints.
Password Complexity
Configure password length, character types (uppercase, lowercase, numbers, special characters), and overall complexity. Strong password rules reduce the risk of brute‑force or credential theft attacks. The following options are available.
- Large letters + small letters + numbers + special characters
- Large letters
- Large letters + small letters
- Large letters + small letters +numbers + special characters
- Not configured
Post Authentication Action
Configure the post-authentication action that you want to enforce post-user authentication. The following options are available.
- Reset password: upon expiry of the grace period, the managed account password will be reset.
- Reset the password and log off the managed account: upon the expiry of the grace period, the managed account password will be reset and any interactive logon session using the managed account will be terminated.
- Rest the password and reboot: upon the expiry of the grace period, the managed account password will be reset and the managed device will be immediately rebooted.
Step 4: On the Assignment page in the Intune admin center, you can assign the Intune LAPS policy to All Devices for broad deployment or to specific Azure AD groups depending on organizational requirements, and to make your Intune LAPS setup more precise you can also apply assignment filters to narrow the deployment scope further—for example, targeting only Windows 11 endpoints or devices in a particular department—ensuring that your configure Intune LAPS deployment delivers secure local administrator password management exactly where it’s needed while maintaining flexibility and alignment with security baselines.
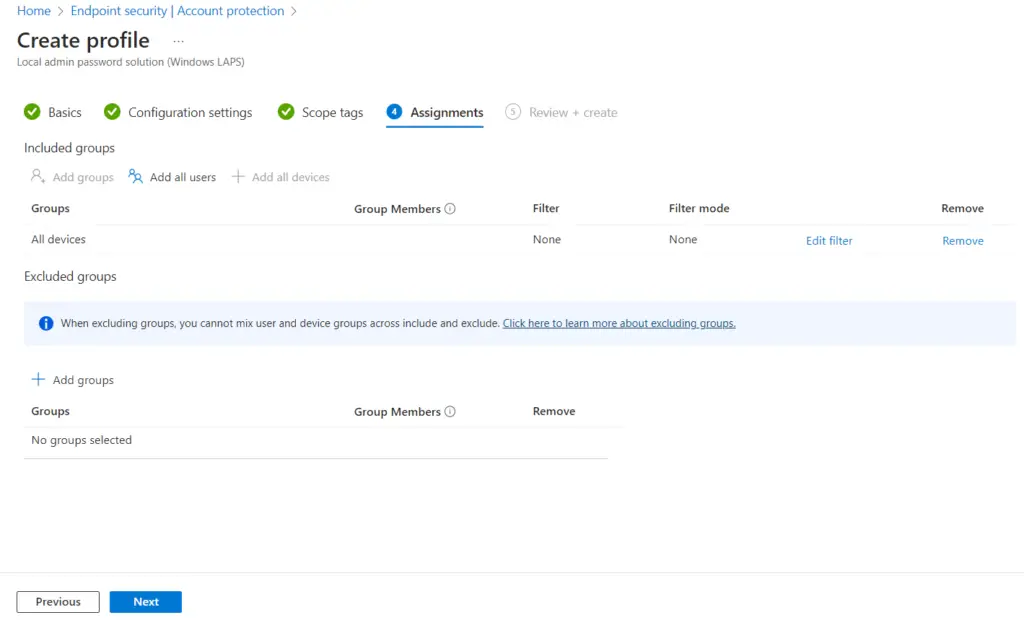
Step 6: On the Review + Create page in the Intune admin center, carefully verify all the details of your Intune LAPS setup—including the policy name, configuration settings such as password complexity and rotation interval, and the assigned device groups or filters—then confirm that everything aligns with your organizational requirements and security baselines; once satisfied, click Create to finalize and deploy the Intune LAPS policy, enabling secure local administrator password management across your Windows 10 and Windows 11 endpoints.
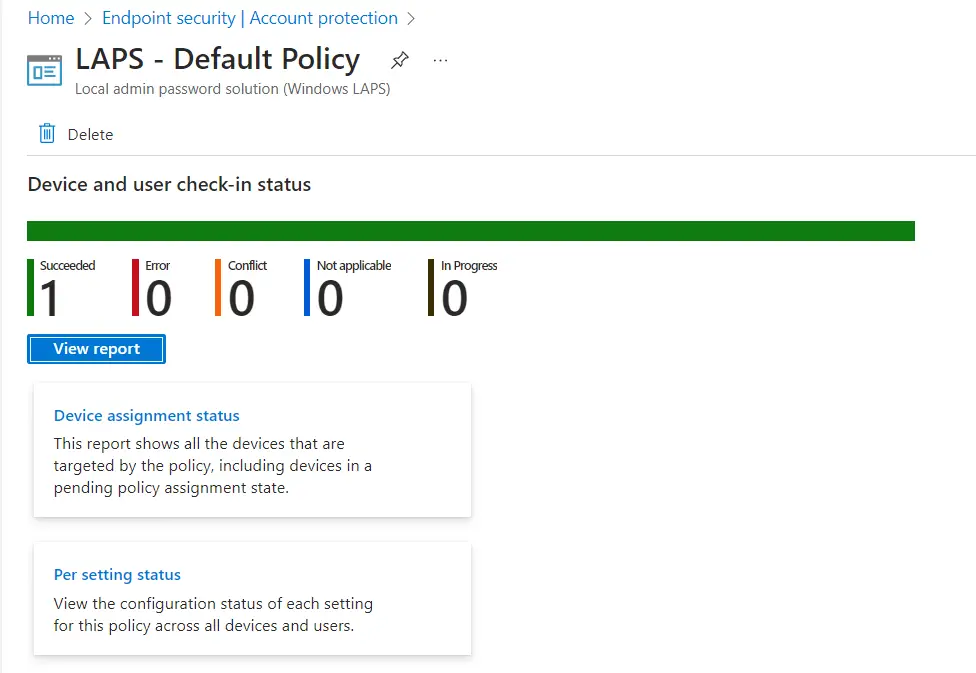
How to Review policy assignments from the Intune console
You can review the policy assignment status from the Endpoint Security / Account protection blade. To see the policy assignment status, simply navigate to Endpoint security / Account protection and select the policy you created for LAPS, and click on View Report to see the compliance status.
You can also check the Device assignment status and Per Setting Status.
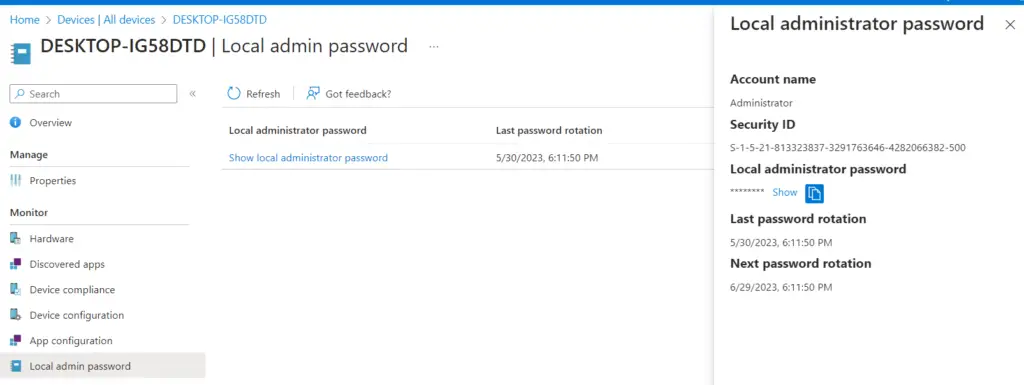
How to Retrieve Local Admin Password for a Device
The local admin account password for managed devices will be backed up in Azure Active Directory. You can view the password for a device from the Microsoft Intune console using the steps below.
- In the Intune console, navigate to Devices / All Devices and select the device for which you need to retrieve the local admin password
- Select Local Admin Password from the left pane
- Click on the Show Local Administrator password link
Review the Windows LAPS policy assignment status on a device
Windows LAPS processes the currently active policy periodically (every hour). To avoid waiting after you apply the policy, you can run the Invoke-LapsPolicyProcessing PowerShell cmdlet. This is usually helpful in testing or troubleshooting, as you can force the policy to run immediately.
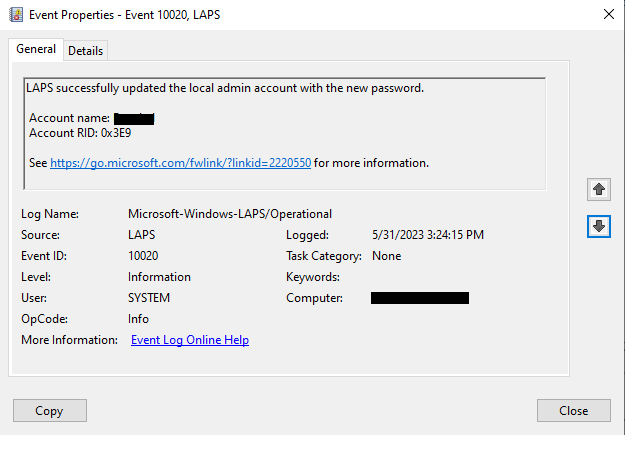
The Windows LAPS event logs can be found in Event Viewer under Event Viewer > Application and Services Log > Microsoft > Windows > LAPS node.
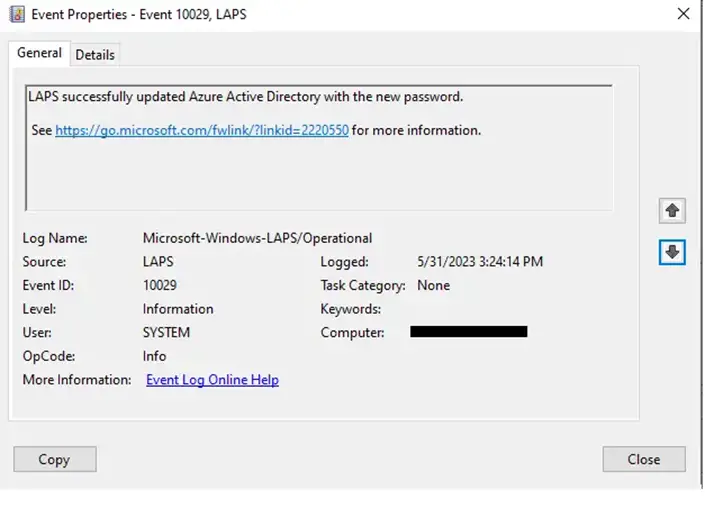
The event log below shows that LAPS successfully updated the local admin account with the new password.
The event log below shows that LAPS successfully updated the Azure Active Directory with the new password.
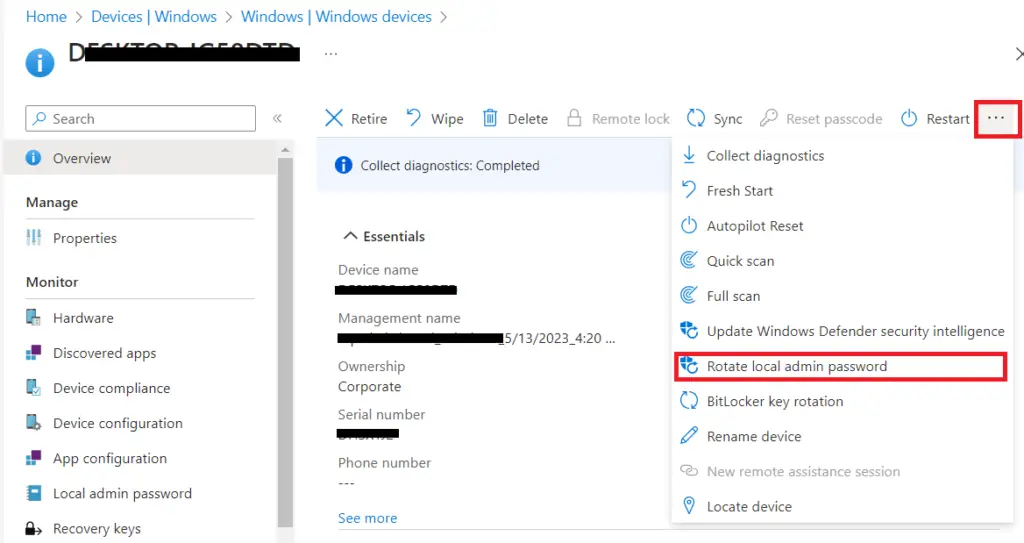
How to rotate local admin password from the Intune console
There may be an ad-hoc requirement to rotate the local admin password / reset the local admin password for a device. The situation may arise due to the disclosure of passwords to unauthorized users, a security breach or other reasons. You can follow the steps below to rotate passwords for an Intune-managed device.
- Navigate to Devices > Windows > Windows Devices and select the Windows device for which you want to rotate the password
- Click on the three dots icon on the right side and select Rotate local admin password
- Click on Yes on the confirmation dialog box.
Conclusion
In conclusion, implementing Windows LAPS with Intune provides a streamlined and secure way to manage local administrator credentials across your environment. By completing the Intune LAPS setup and carefully configuring policies for password complexity, rotation intervals, and account selection, organizations can ensure automated password rotation and compliance with security baselines. Assigning policies to the right Azure AD groups and using filters makes the deployment flexible, while RBAC roles simplify password retrieval without compromising security. Ultimately, when you configure Intune LAPS, you gain centralized control, reduce the risk of credential theft, and strengthen endpoint protection across Windows 10 and Windows 11 devices—making LAPS Intune integration a critical component of modern endpoint security.
Related Posts
- Block USB Device Access with Exceptions | Microsoft Intune
- Deny Write Access to USB Devices Using Intune Catalog Settings
- Manage Windows Local Administrator Password with Intune & Windows LAPS
- Check OS Version Compliance with Device Compliance Policy & Notify User | Microsoft Intune
- How to manage the local administrators group on Azure AD joined devices | Intune
Subscribe to Techuisitive Newsletter
Be the first to know about our new blog posts. Get our newsletters directly in your inbox and stay up to date about Modern Desktop Management technologies & news.