Deploying Win32 apps in Microsoft Intune isn’t just about packaging and pushing software—it’s about ensuring the right conditions are met before installation. Intune’s Requirements Rules give admins precise control, from verifying OS architecture to checking disk space, registry keys, or custom PowerShell scripts. In this guide, we’ll break down each requirement type, show real‑world examples, and explain how to troubleshoot using Intune logs.
For step‑by‑step instructions on creating a Win32 application in Microsoft Intune, please refer to the dedicated blog post.
Table of contents
Win32 App Requirements Checklist
Before deploying Win32 applications with Microsoft Intune, it’s essential to confirm that all requirement rules are properly configured. These rules determine whether an app is applicable to a device, based on factors like OS architecture, minimum version, hardware resources, registry keys, or custom scripts. A quick checklist helps administrators validate settings, avoid deployment errors, and streamline troubleshooting.
- ✅ Configure mandatory OS architecture & minimum OS version
- ✅ Set optional rules (disk space, RAM, CPU speed, processors)
- ✅ Add extended rules (File, Registry, Script) as needed
- ✅ Verify applicability in IntuneManagementExtension.log
- ✅ Troubleshoot failures with log excerpts
Win32 App – Mandatory Requirement
When creating a Win32 app in Microsoft Intune, you must configure the following mandatory requirement rules:
Operating System Architecture:
Select the architecture(s) required for installation.
Options: 32‑bit or 64‑bit
Minimum Operating System Version:
Define the lowest supported Windows version for the app.
Options: Windows 10, version 1607 and above
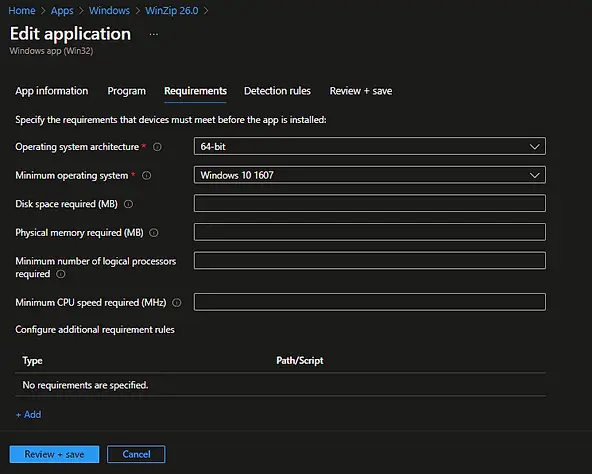
Win32 App – Optional Requirement
In addition to mandatory rules, you can configure optional requirement rules in Microsoft Intune to control app installation based on device resources:
Minimum CPU Speed (MHz): Specify the minimum processor speed required.
Disk Space Required (MB): Specify the minimum free disk space needed on the system drive. Example: 1000 MB
Physical Memory Required (MB): Define the minimum RAM required for installation. Example: 4096 MB
Minimum Number of Logical Processors: Set the minimum number of logical processors required to run the app.
Win32 App – Additional Requirement Rules
Additional requirement rules provide extended options to configure Win32 app deployment in Microsoft Intune. These rules allow administrators to validate app installation conditions beyond the mandatory and optional checks.
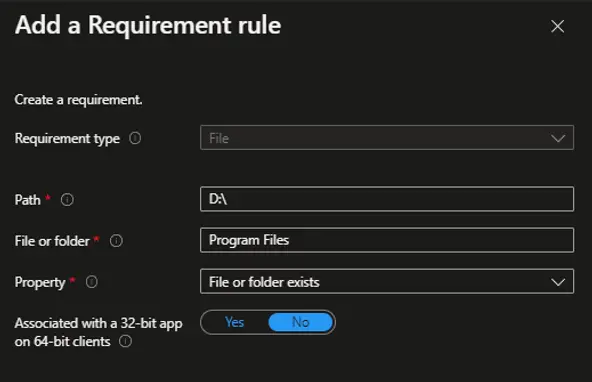
Requirement Types: File
The File requirement rule Validates based on file or folder existence, date, version, or size. Example: Ensure a specific .exe file exists before installation.
How to Add a File‑Based Requirement Rule:
Configure the file path and condition (existence, version, size, or date).
Navigate to the Requirements page while creating or editing the Win32 app.
Click + Add at the bottom of the page.
Select File from the Requirement type options.
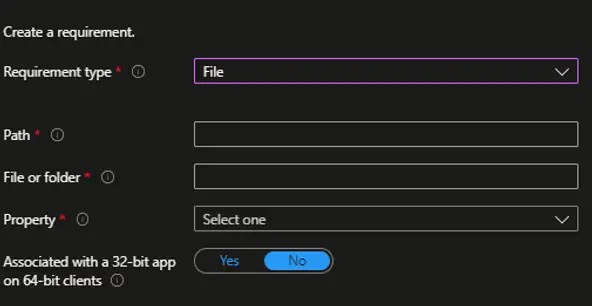
You have to provide the following details when using this Requirement Rule.
- Path: Enter the full path of the folder that contains the file or folder to detect.
- File or folder: Enter the file or folder to detect.
- Property: Select the type of rule used to validate the presence of the app.
- File or folder exists
- Date modified
- Date created
- String (version)
- Size in MB
Requirement Type: Registry
The Registry requirement rule allows administrators to validate Win32 app installation conditions in Microsoft Intune based on registry settings. This can include:
- Key existence – Verify if a specific registry key is present.
- String comparison – Match or compare registry string values.
- Version checks – Validate application or system versions stored in the registry.
How to Add a Registry‑Based Requirement Rule:
Configure the registry path, value, and condition (existence, comparison, or version).
Navigate to the Requirements page while configuring the Win32 app.
Click + Add at the bottom of the page.
Select Registry from the Requirement type options.
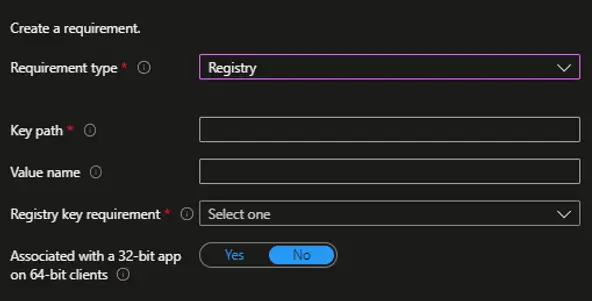
You have to provide the following details when using this detection rule.
- Key path: The full path of the registry key that contains the value to detect.
- Value name: The name of the registry value to detect. If this value is empty, the detection will happen on the key. The (default) value of a key will be used as the detection value if the detection method is other than file or folder existence.
- Registry key requirement: Select the type of registry key comparison that’s used to validate the presence of the app. The following comparison types are available.
- Key exists
- The key does not exist
- String comparison
- Version comparison
- Integer comparison
Requirement Type: Script
The Script requirement rule provides advanced options to evaluate Win32 app installation conditions in Microsoft Intune that cannot be validated using file or registry checks. With this rule, administrators can use a PowerShell script to determine whether an application should install, based on custom logic.
Common Use Cases:
- Validate complex conditions (e.g., device type, custom configurations).
- Check for specific values or states not available via file/registry rules.
- Implement organization‑specific compliance checks before deployment.
How to Add a Script‑Based Requirement Rule:
Upload or paste the PowerShell script and define the evaluation logic.
Navigate to the Requirements page while configuring the Win32 app.
Click + Add at the bottom of the page.
Select Script from the Requirement type options.
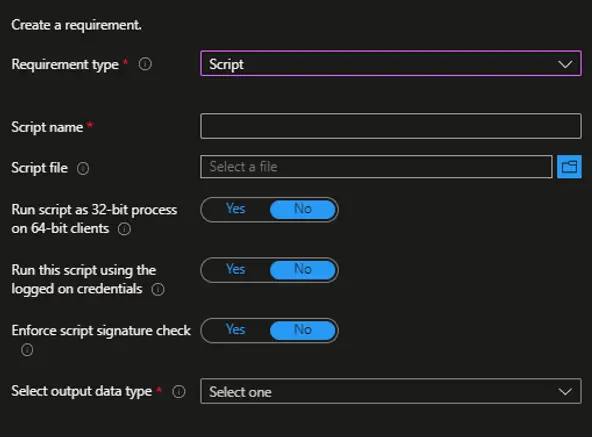
We have to provide the following mandatory details when using script requirement rules.
- Script Name: Enter the name of the Script. For example, check Disk Space
- Script File: Click on the Browse button and select the script file.
- Select Output Data Type: Select the output data type. The following output data types are currently available.
- String
- Date and Time
- Integer
- Floating Point
- Version
- Boolean
Win32 App – Monitoring Requirement Rule Behavior
Now that we understand how requirement rules are evaluated on the client side, it’s important to know how to monitor their behavior during Win32 app deployment in Microsoft Intune.
All details related to Win32 app installation and requirement evaluation are logged in the IntuneManagementExtension.log file. By analyzing this log, administrators can decode the exact steps Intune takes when validating requirements.
While you typically don’t need to review logs during a successful deployment, this information becomes invaluable when troubleshooting deployment failures, requirement mismatches, or applicability issues.
Key Takeaway:
Reviewing logs helps identify why an app failed to install or was marked as not applicable.
Requirement rules are always evaluated at the client end.
The IntuneManagementExtension.log provides step‑by‑step visibility into requirement checks.
Monitoring Mandatory / Optional Requirements Rules Evaluation
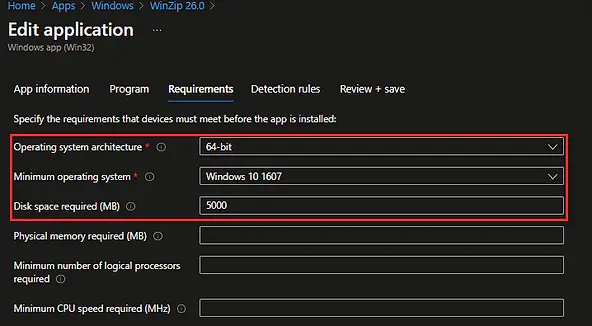
We have configured both mandatory and optional requirements here.
Operating System architecture: 64-bit
Minimum operating system: Windows 10 1607
Disk space required: 5000 MB
When the application installation is initiated through the Company Portal, the configured requirement rules are quickly logged in the Intune Management Extension under the Check Applicability section.
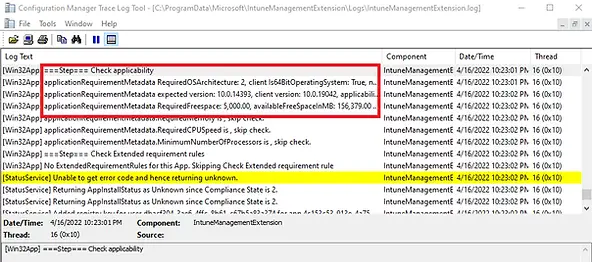
Below are complete excerpts from the IntuneManagementExtension.log that capture the Check Applicability section during a Win32 app deployment. These entries show how requirement rules are evaluated on the client device, including whether the app meets the configured mandatory, optional, file, registry, or script‑based conditions.
Reviewing these logs helps administrators:
Troubleshoot deployment failures linked to requirement rules.
Understand the step‑by‑step evaluation process.
Identify why an app was marked as applicable or not applicable.
<![LOG[[Win32App] ===Step=== Check applicability]LOG]!><time="22:23:01.9740518" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="16" file="">
<![LOG[[Win32App] applicationRequirementMetadata RequiredOSArchitecture: 2, client Is64BitOperatingSystem: True, nativeMachine IsArm64: False, applicability: Applicable.]LOG]!><time="22:23:01.9825346" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="16" file="">
<![LOG[[Win32App] applicationRequirementMetadata expected version: 10.0.14393, client version: 10.0.19042, applicability: Applicable.]LOG]!><time="22:23:02.0233144" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="16" file="">
<![LOG[[Win32App] applicationRequirementMetadata RequiredFreespace: 5,000.00, availableFreeSpaceInMB: 156,379.00 on Drive C:\, applicability: Applicable.]LOG]!><time="22:23:02.0869701" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="16" file="">
<![LOG[[Win32App] applicationRequirementMetadata.RequiredMemory is , skip check.]LOG]!><time="22:23:02.0879780" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="16" file="">
<![LOG[[Win32App] applicationRequirementMetadata.RequiredCPUSpeed is , skip check.]LOG]!><time="22:23:02.0879780" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="16" file="">
<![LOG[[Win32App] applicationRequirementMetadata.MinimumNumberOfProcessors is , skip check.]LOG]!><time="22:23:02.0889723" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="16" file="">
Monitoring File Requirement Rules Evaluation
We configured the following requirement rule: the application will install only if the D:\Program Files folder exists.
The IntuneManagementExtension.log confirms that the requirement rule was evaluated and the specified folder exists. As a result, the requirement was successfully met, allowing the application installation to proceed.
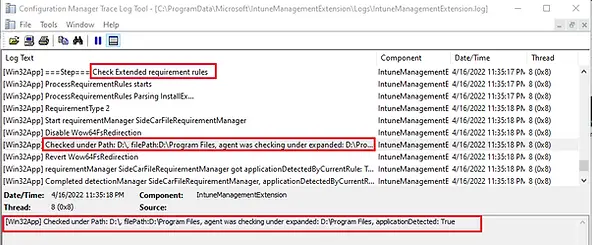
Below are complete excerpts from the IntuneManagementExtension.log that capture the Check Extended Requirement section during a Win32 app deployment. These entries illustrate how Intune evaluates extended requirement rules such as File, Registry, and Script‑based checks on the client device.
<![LOG[[Win32App] ===Step=== Check Extended requirement rules]LOG]!><time="23:35:17.6812330" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] ProcessRequirementRules starts]LOG]!><time="23:35:17.6821853" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] ProcessRequirementRules Parsing InstallEx...]LOG]!><time="23:35:17.6821853" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] RequirementType 2]LOG]!><time="23:35:18.1737361" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] Start requirementManager SideCarFileRequirementManager]LOG]!><time="23:35:18.1747403" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] Disable Wow64FsRedirection]LOG]!><time="23:35:18.5346625" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] Checked under Path: D:\, filePath:D:\Program Files, agent was checking under expanded: D:\Program Files, applicationDetected: True]LOG]!><time="23:35:18.5359328" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] Revert Wow64FsRedirection]LOG]!><time="23:35:18.5369375" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] requirementManager SideCarFileRequirementManager got applicationDetectedByCurrentRule: True as system]LOG]!><time="23:35:18.5379325" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] Completed detectionManager SideCarFileRequirementManager, applicationDetectedByCurrentRule: True]LOG]!><time="23:35:18.5379325" date="4-16-2022" component="IntuneManagementExtension" context="" type="1" thread="8" file="">
<![LOG[[Win32App] Extended requirement rules processing complete. isApplicationApplicable: Applicable]LOG]!
Monitoring Registry requirement rules Evaluation
The behavior of registry‑based requirement rules is almost identical to file or folder‑based rules, as both validate the existence or properties of specific system resources before allowing application installation.
Monitoring Script Requirement Rules Evaluation
For this deployment scenario, we considered the following requirement:
The application must be installed on the D: drive, but the requirement rule is configured to ensure that the D: drive is not a CD/DVD or removable storage device. This validation is achieved using a PowerShell script, which checks the drive type before allowing installation.
Key Points:
If the script fails or returns false, the app is marked as not applicable.
Script rules extend Intune’s flexibility beyond file or registry checks.
PowerShell can validate custom conditions such as drive type, device configuration, or organizational policies.
If the script returns a positive result (e.g., confirming D: is a fixed drive), the requirement is met and installation proceeds.
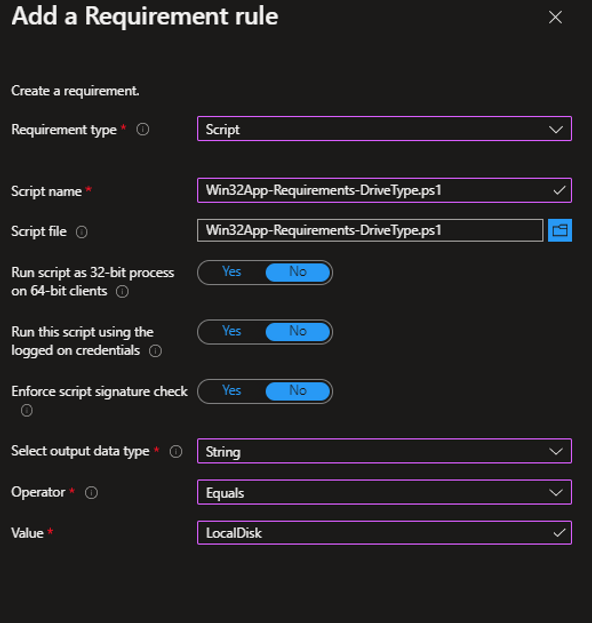
Here is the PowerShell script we used to validate custom Intune Win32 app requirements. The script checks whether the D: drive is a local disk. It writes the output to STDOUT, and the requirement rule is configured to confirm that the returned value equals "LocalDisk".
foreach ($drive in $ldisk)
{
if ($drive.DeviceID -eq "D:") {
if ($drive.DriveType -eq 3)
{Write-Host "LocalDisk"
Exit}
else
{ Write-Host "NotLocalDisk"
Exit}
}
}
Write-Host "DriveNotFound"
The IntuneManagementExtension.log confirms that the requirement rule was evaluated, the PowerShell script executed successfully, and the value "LocalDisk" was returned. Therefore, the requirement was met, and the application installation proceeded as expected.
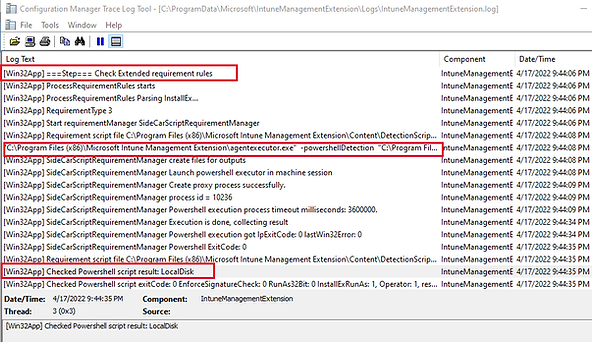
Here are the excerpts from IntuneManagementExtension log for Check Extended requirements.
<![LOG[[Win32App] ===Step=== Check Extended requirement rules]LOG]!><time="21:44:06.4435116" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] ProcessRequirementRules starts]LOG]!><time="21:44:06.4445104" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] ProcessRequirementRules Parsing InstallEx...]LOG]!><time="21:44:06.4465216" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] RequirementType 3]LOG]!><time="21:44:06.4465216" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] Start requirementManager SideCarScriptRequirementManager]LOG]!><time="21:44:06.5614100" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] Requirement script file C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1 is saved.]LOG]!><time="21:44:08.4243079" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG["C:\Program Files (x86)\Microsoft Intune Management Extension\agentexecutor.exe" -powershellDetection "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1" "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1quotedResultFilePath.txt" "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1quotedErrorFilePath.txt" "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1quotedTimeoutFilePath.txt" 3600 "C:\Windows\System32\WindowsPowerShell\v1.0" 0 "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1quotedExitCodeFilePath.txt" False]LOG]!><time="21:44:08.9273914" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] SideCarScriptRequirementManager create files for outputs]LOG]!><time="21:44:08.9273914" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] SideCarScriptRequirementManager Launch powershell executor in machine session]LOG]!><time="21:44:08.9313818" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] SideCarScriptRequirementManager Create proxy process successfully.]LOG]!><time="21:44:09.1625970" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] SideCarScriptRequirementManager process id = 10236]LOG]!><time="21:44:09.1636001" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] SideCarScriptRequirementManager Powershell execution process timeout milliseconds: 3600000.]LOG]!><time="21:44:09.1636001" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] SideCarScriptRequirementManager Execution is done, collecting result]LOG]!><time="21:44:34.4877644" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] SideCarScriptRequirementManager Powershell execution got lpExitCode: 0 lastWin32Error: 0]LOG]!><time="21:44:34.4887625" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] SideCarScriptRequirementManager Powershell ExitCode: 0]LOG]!><time="21:44:35.1416076" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] Requirement script file C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1quotedExitCodeFilePath.txt is deleted.]LOG]!><time="21:44:35.1427095" date="4-17-2022" component="IntuneManagementExtension" context="" type="1" thread="3" file="">
<![LOG[[Win32App] Checked Powershell script result: LocalDisk
Conclusion
By mastering Win32 app requirements rules in Microsoft Intune, administrators can ensure that applications install only under the right conditions—whether based on OS architecture, minimum version checks, disk space, registry keys, or custom PowerShell scripts. Proper configuration of mandatory and optional rules reduces deployment errors, improves compliance, and streamlines endpoint management. Combined with effective use of IntuneManagementExtension logs for troubleshooting, these rules give IT teams precise control over application deployment, device targeting, and user experience. Leveraging Intune’s flexibility helps organizations achieve more reliable modern management and secure Windows app delivery.
Related Posts
- Deploy Win32 App Using Intune Enterprise App Catalog
- Understanding Win32 App Detection Rules
- Understanding Win32 App Requirements Rule
- Upgrade / Replace Win32 Apps with Supersedence Relationship
- Win32 App Deployment with Dependencies
- Win32 Apps vs LOB Apps
- Win32 App Deployment failed with error code 0x80070643
- Win32 App Deployment Failed with Error 0x87D1041C
- Win32 App Deployment failed with error 0x87D300C9
- Win32 App failed with error code 0x80070653
- Deploy Google Chrome for Enterprise with Intune Win32 App
- How to Prepare Win32 App Installation source for Microsoft Intune
- SCCM Device Collection Equivalents in Microsoft Intune for App Deployment
- Deploy Microsoft SQL Server Management Studio 19.02 through Intune
- Organizing Laptop and Desktop in Intune Using Filters
Subscribe to Techuisitive Newsletter
Be the first to know about our new blog posts. Get our newsletters directly in your inbox and stay up to date about Modern Desktop Management technologies & news.