Win32 app detection rules in Microsoft Intune are critical for ensuring accurate application deployment and compliance. These rules determine whether an app is already installed, when it should be offered, and how uninstall actions are triggered. In this guide, we’ll break down the different detection methods—MSI, file, registry, and custom PowerShell scripts—along with practical examples and log snippets to help administrators configure and troubleshoot Intune deployments effectively.
Win32 app detection rules in Intune are methods used to verify whether an application is installed and compliant on a managed device. They prevent duplicate installations, ensure accurate deployment status, and support troubleshooting through MSI, file, registry, or PowerShell checks.
- Explore Intune Win32 App Detection Rules
- Manually Configure Intune App Detection Rule
- Use a custom detection Rule
- Conclusion
- Frequently Asked Questions (FAQs)
- What are Win32 app detection rules in Intune?
- Which types of detection rules does Intune support?
- When should I use MSI detection rules?
- How do file and registry detection rules work?
- Can I use PowerShell scripts for detection?
- Where can I find logs for troubleshooting detection rules?
- What happens if detection rules are misconfigured?
- Related Posts
Explore Intune Win32 App Detection Rules
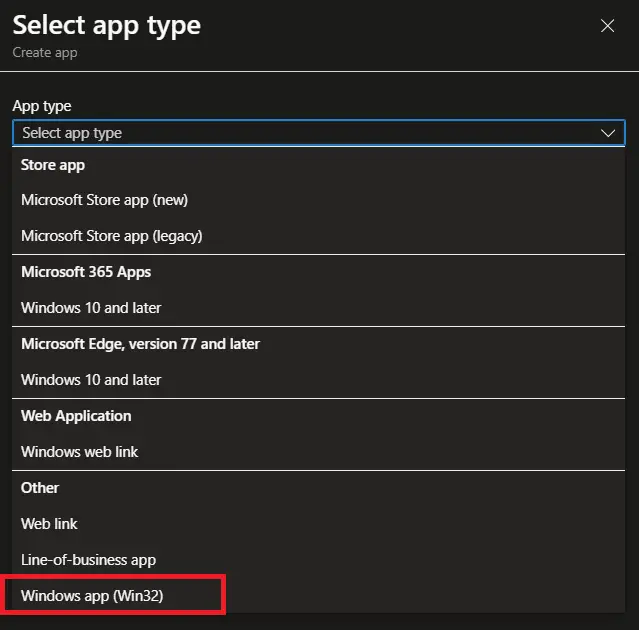
To explore the Win32 app detection rules in Microsoft Intune, open the Intune admin center and navigate to: Apps > Windows > Windows apps. Select any Win32 application, then go to Properties > Detection rules to access the Detection Rules blade.
Note: You have to create a Win32 app if you don’t have one. Check this article if you want to know how to deploy a Win32 app.
The following Win32 app detection rule formats are available in Microsoft Intune:
Use custom detection rules: This option enables administrators to create detection logic using a custom PowerShell script, providing flexibility for complex scenarios that cannot be handled by built‑in methods.
Manually configure detection rules: This option allows Intune administrators to define detection logic based on MSI product codes, file or folder existence, file version, or registry keys and values.
Manually Configure Intune App Detection Rule
Let’s take a closer look at how to manually configure Intune detection rules. This detection rule format supports three options: MSI‑based detection, file‑based detection, and registry‑based detection. Each method allows administrators to define how Intune verifies whether a Win32 application is installed or meets specific conditions.
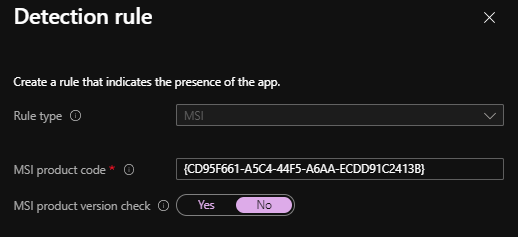
1. MSI Product-Based Win32 App Detection Rules
This detection rule detects application installation based on the MSI product key or version check. When you choose this rule type, you have two settings:
- MSI product code: This property allows the administrator to configure the MSI product code to detect the installation of the App. When you use this rule type with an MSI, the MSI product key is populated automatically.
- MSI product version check: This property allows the administrator to configure an additional check that is a specific version of the MSI product code to detect the application.
Example of MSI product detection:
Check for app existence based on MSI product code
To add a Win32 app detection rule based on an MSI product code in Microsoft Intune, configure the detection settings by selecting the following options:
- Rule type: MSI
- MSI product code: Enter MSI product code
- MSI product version check: No
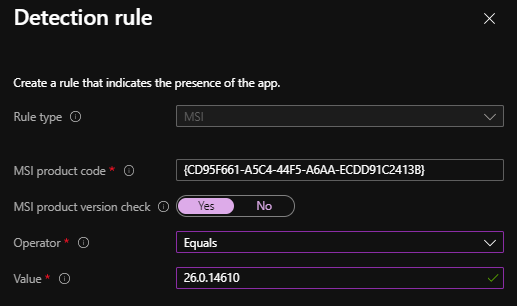
Check for app existence based on product code and version
To add a Win32 app detection rule based on an MSI product code and version in Microsoft Intune, configure the detection settings by selecting the following options:
- Rule type: MSI
- MSI product code: Enter MSI product code
- MSI product version check: Yes
- Operator / Value: Select operator and enter product version
Client-side activities:
Every step of the Win32 app installation process in Microsoft Intune is recorded in the Intune Management Extension log file, located at:
C:\ProgramData\Microsoft\IntuneManagementExtension\LogsThis includes activities such as downloading policies for detection and installation. In this article, we’ll focus specifically on policy processing and detection rules.
The following snippets from IntuneManagementExtension.log illustrate the details of the policies received by a client, including the associated Intune Win32 app detection rules.
Client Received Policy:
Get policies = [{"Id":"4c153c53-913e-4a75-92b1-27e53ca03876","Name":"WinZip 26.0","Version":1,"Intent":3,"TargetType":2,"AppApplicabilityStateDueToAssginmentFilters":null,"AssignmentFilterIds":null,"DetectionRule":"[{\"DetectionType\":1,\"DetectionText\":\"{\\\"ProductCode\\\":\\\"{CD95F661-A5C4-44F5-A6AA-ECDD91C2413B}\\\",\\\"ProductVersion\\\":\\\"26.0.14610\\\",\\\"ProductVersionOperator\\\":1}\"}]","InstallCommandLine":"msiexec /i winzip260-64.msi /qn INSTALLDIR=\"D:\\Program Files\\WinZip26\"","UninstallCommandLine":"msiexec /x \"
Detection Phase:
During the Win32 app detection rules phase in Microsoft Intune, each detection rule is evaluated and logged. In the example above, DetectionType 1 represents an MSI‑based detection rule. The log entries show that the application detection failed because the app was not installed on the client device.
<![LOG[[Win32App] ===Step=== Detection rules]LOG]!><time="19:32:56.1219769" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] ProcessDetectionRules starts]LOG]!><time="19:32:56.1229716" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] ProcessDetectionRules Parsing InstallEx...]LOG]!><time="19:32:56.1229716" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] DetectionType 1]LOG]!><time="19:32:56.1239684" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] Start detectionManager SideCarProductCodeDetectionManager]LOG]!><time="19:32:56.1249660" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[CheckProductCodeExists fails with product code {CD95F661-A5C4-44F5-A6AA-ECDD91C2413B}, errorCode = 1605, try without brace]LOG]!><time="19:32:56.1259630" date="2-22-2022" component="IntuneManagementExtension" context="" type="2" thread="21" file=""> <![LOG[CheckProductCodeExists fails with product code CD95F661-A5C4-44F5-A6AA-ECDD91C2413B, errorCode = 87]LOG]!><time="19:32:56.1259630" date="2-22-2022" component="IntuneManagementExtension" context="" type="3" thread="21" file=""> <![LOG[[Win32App] Checked ProductCode {CD95F661-A5C4-44F5-A6AA-ECDD91C2413B}, Cannot find, applicationDetected: False]LOG]!><time="19:32:56.1273728" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file="">
Post Application Installation Phase:
Since the application was not detected during the Win32 app detection phase in Microsoft Intune, it will be offered to the client for installation. After the installation completes, the same detection rules are evaluated again to verify the application’s presence on the device and confirm a successful deployment.
<![LOG[[Win32App] ===Step=== Detection rules after Execution]LOG]!><time="19:36:24.5691438" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] ProcessDetectionRules starts]LOG]!><time="19:36:24.5691438" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] ProcessDetectionRules Parsing InstallEx...]LOG]!><time="19:36:24.5701379" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] DetectionType 1]LOG]!><time="19:36:24.5711353" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] Start detectionManager SideCarProductCodeDetectionManager]LOG]!><time="19:36:24.5721336" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] Equal: actualValue: 26.0.14610, compareValue: 26.0.14610, applicationDetected: True]LOG]!><time="19:36:24.5721336" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] detectionManager SideCarProductCodeDetectionManager got applicationDetectedByCurrentRule: True as system]LOG]!><time="19:36:24.5731672" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] Completed detectionManager SideCarProductCodeDetectionManager, applicationDetectedByCurrentRule: True]LOG]!><time="19:36:24.5731672" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file="">
2. File-Based Win32 App Detection Rules
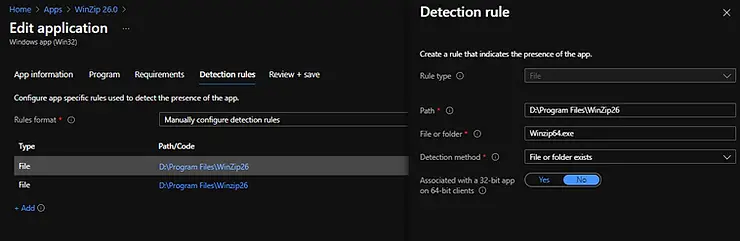
Win32 app detection rules in Microsoft Intune can verify application presence based on file or folder existence, file version, date, or size. When configuring a file‑based detection rule, administrators need to provide specific details such as the file path, file or folder name, and the detection criteria (e.g., version, date, or size). These parameters allow Intune to accurately determine whether the targeted application is installed on the device.
You need to provide the following details when configuring a file-based detection rule.
- Path: Enter the full path of the folder that contains the file or folder to detect.
- File or folder: Enter the file or folder to detect.
- Detection method: Select the type of detection method used to validate the app’s presence.
- File or folder exists
- Date modified
- Date created
- String (version)
- Size in MB
A Win32 app detection rule in Microsoft Intune can include multiple file‑based detection checks. When more than one detection rule is configured for an application, all rule evaluations must return true for the app to be successfully detected on the client device.
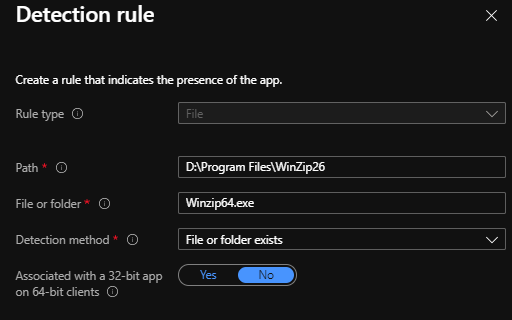
Example of File-based detection:
Check for file existence: You need to provide the following details.
- Rule type: File
- Path: File path
- File or folder: Name of file or folder
- Detection method: Select the type of detection method used to validate the app’s presence.
Check for the file version:

Client-side activities:
This section demonstrates how to view client‑side activities in the Intune Management Extension log. In the log snippets below, you can see that the client downloaded the latest policy from Microsoft Intune, which contains all the application details, including the detection rules configured in the Intune portal.
In this example, DetectionType 2 represents a File/Folder‑based detection rule.
Get policies = [{"Id":"4c153c53-913e-4a75-92b1-27e53ca03876","Name":"WinZip 26.0","Version":1,"Intent":3,"TargetType":2,"AppApplicabilityStateDueToAssginmentFilters":null,"AssignmentFilterIds":null,"DetectionRule":"[{\"DetectionType\":2,\"DetectionText\":\"{\\\"Path\\\":\\\"D:\\\\\\\\Program Files\\\\\\\\WinZip26\\\",\\\"FileOrFolderName\\\":\\\"Winzip64.exe\\\",\\\"Check32BitOn64System\\\":false,\\\"DetectionType\\\":1,\\\"Operator\\\":0,\\\"DetectionValue\\\":null}\"},
{\"DetectionType\":2,\"DetectionText\":\"{\\\"Path\\\":\\\"D:\\\\\\\\Program Files\\\\\\\\Winzip26\\\",\\\"FileOrFolderName\\\":\\\"Winzip64.exe\\\",\\\"Check32BitOn64System\\\":false,\\\"DetectionType\\\":4,\\\"Operator\\\":1,\\\"DetectionValue\\\":\\\"50.260.14610.0\\\"}\"}]","InstallCommandLine":"msiexec /i winzip260-64.msi /qn INSTALLDIR=\"D:\\Program Files\\WinZip26\"","UninstallCommandLine":"msiexec /x \"{CD95F661-A5C4-44F5-A6AA-ECDD91C2413B}\" /q","RequirementRules":" ........
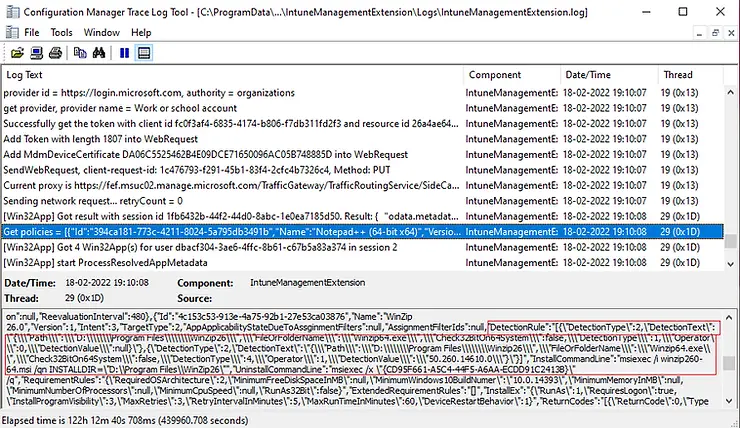
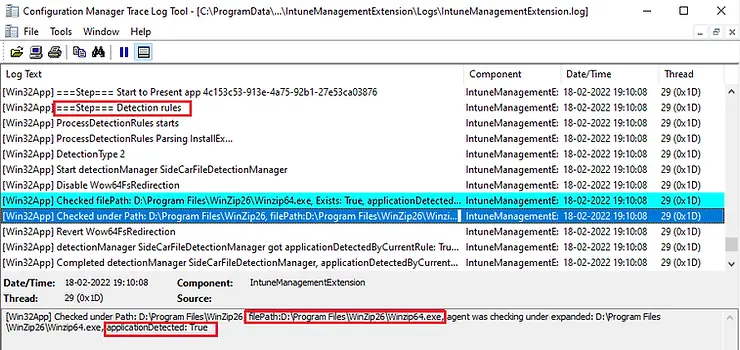
The Win32 app detection rules process in Microsoft Intune begins by evaluating each defined rule. In the example below, we configured two file‑based detection rules:
- File existence check – verifies whether the specified file or folder is present.
- File version check – validates the version of the file against the defined criteria.
For the application to be detected as installed, both rules must evaluate to true. As shown in the IntuneManagementExtension.log, the system first checks the file or folder existence rule before proceeding to the file version rule.
[Win32App] Checked filePath: D:\Program Files\WinZip26\Winzip64.exe, Exists: True, applicationDetected: True [Win32App] Checked under Path: D:\Program Files\WinZip26, filePath:D:\Program Files\WinZip26\Winzip64.exe, agent was checking under expanded: D:\Program Files\WinZip26\Winzip64.exe, applicationDetected: True
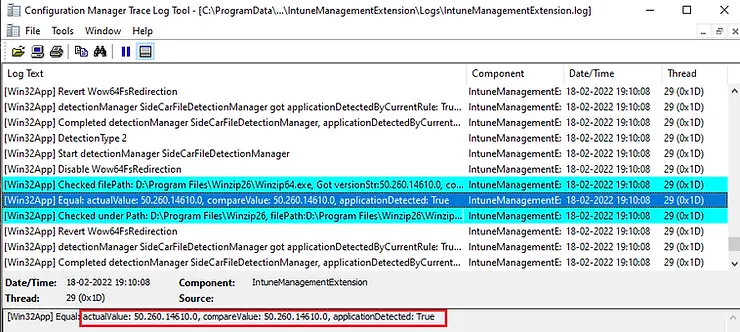
Next, the system validated the second file‑based detection rule by comparing the version installed on the client device with the version specified in the detection rule. Since both conditions were evaluated to true, the application was successfully detected on the computer and will not be re‑offered for installation.
[Win32App] Checked filePath: D:\Program Files\Winzip26\Winzip64.exe, Got versionStr:50.260.14610.0, compareValue 50.260.14610.0 [Win32App] Equal: actualValue: 50.260.14610.0, compareValue: 50.260.14610.0, applicationDetected: True [Win32App] Checked under Path: D:\Program Files\Winzip26, filePath:D:\Program Files\Winzip26\Winzip64.exe, agent was checking under expanded: D:\Program Files\Winzip26\Winzip64.exe, applicationDetected: True
3. Registry-Based Win32 App Detection Rules
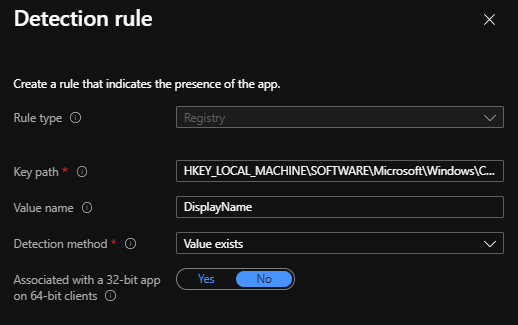
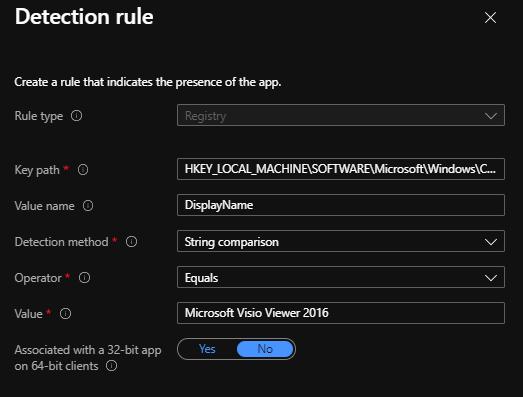
Intune Win32 app detection rule registry verifies an application’s presence by checking specific Windows registry keys and values. Administrators can configure detection based on key existence, string or integer values, or version comparisons, making this method useful for applications that store installation details in the registry.
- Key path: The full path of the registry key that contains the value to detect.
- Value name: The name of the registry value to detect. If this value is empty, the detection will happen on the key. If the detection method is other than file or folder existence,the (default) value of a key will be used as the detection value
- Detection method: Select the type of detection method that’s used to validate the presence of the app. The following detection methods are available in registry-based detection rules.
- Key exists
- The key does not exist
- String comparison
- Version comparison
- Integer comparison
Example of Registry-based detection:
Please see the Intune registry detection rule example in the screenshot below.
Check for string comparison:
Client-side activities:
Similar to MSI‑based and file‑based detection rules, the details of a registry‑based detection rule are included in the policy downloaded by the client. In the log entries, DetectionType 0 represents a registry‑based detection rule, which verifies application presence through registry keys and values.
Get policies = [{"Id":"c9b949c9-6e56-4e3a-a9d5-7f174fd5681c","Name":"visioviewer_4339-1001_x64_en-us.exe","Version":1,"Intent":3,"TargetType":2,"AppApplicabilityStateDueToAssginmentFilters":0,"AssignmentFilterIds":["40a00a67-5909-47bd-8948-54dc237881e6"],"DetectionRule":"[{\"DetectionType\":0,\"DetectionText\":\"{\\\"Check32BitOn64System\\\":0,\\\"Path\\\":\\\"HKEY_LOCAL_MACHINE\\\\\\\\SOFTWARE\\\\\\\\Microsoft\\\\\\\\Windows\\\\\\\\CurrentVersion\\\\\\\\Uninstall\\\\\\\\{95160000-0052-0409-1000-0000000FF1CE}\\\",\\\"KeyName\\\":\\\"DisplayName\\\",\\\"DetectionType\\\":3,\\\"Operator\\\":1,\\\"DetectionValue\\\":\\\"Microsoft Visio Viewer 2016\\\"}\"}]","InstallCommandLine":"visioviewer_4339-1001_x64_en-us.exe /quiet","UninstallCommandLine":"visioviewer_4339-1001_x64_en-us /uninstall /quiet","RequirementRules":"
Once the client receives the deployment policy, it begins processing the application installation workflow. All activities related to Win32 app detection are captured in the Intune Management Extension log. The log snippets below illustrate how the client evaluates detection rules during this phase.
<![LOG[[Win32App] Start detectionManager SideCarRegistryDetectionManager]LOG]!><time="19:36:29.8759872" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[RegistryKeyOrValueExistsFullPath NOT Check32BitOn64, baseReg HKEY_LOCAL_MACHINE]LOG]!><time="19:36:30.0071701" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[RegistryKeyExistsFullPath opening full path HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{95160000-0052-0409-1000-0000000FF1CE}...]LOG]!><time="19:36:30.0121586" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[RegistryKeyExistsFullPath NOT Check32BitOn64, baseReg HKEY_LOCAL_MACHINE]LOG]!><time="19:36:30.0121586" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[RegistryKeyExistsFullPath opening subPath SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{95160000-0052-0409-1000-0000000FF1CE}]LOG]!><time="19:36:30.0121586" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] Got reg value path: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{95160000-0052-0409-1000-0000000FF1CE}, name: DisplayName, value: Microsoft Visio Viewer 2016]LOG]!><time="19:36:30.0121586" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] Equal: actualValue: Microsoft Visio Viewer 2016, DetectionValue: Microsoft Visio Viewer 2016, applicationDetected: True]LOG]!><time="19:36:30.0121586" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] Checked reg path: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{95160000-0052-0409-1000-0000000FF1CE}, name: DisplayName, operator: 1, type: 3, value: Microsoft Visio Viewer 2016 , result of applicationDetected: True]LOG]!><time="19:36:30.0131559" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] detectionManager SideCarRegistryDetectionManager got applicationDetectedByCurrentRule: True as system]LOG]!><time="19:36:30.0131559" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file=""> <![LOG[[Win32App] Completed detectionManager SideCarRegistryDetectionManager, applicationDetectedByCurrentRule: True]LOG]!><time="19:36:30.0131559" date="2-22-2022" component="IntuneManagementExtension" context="" type="1" thread="21" file="">
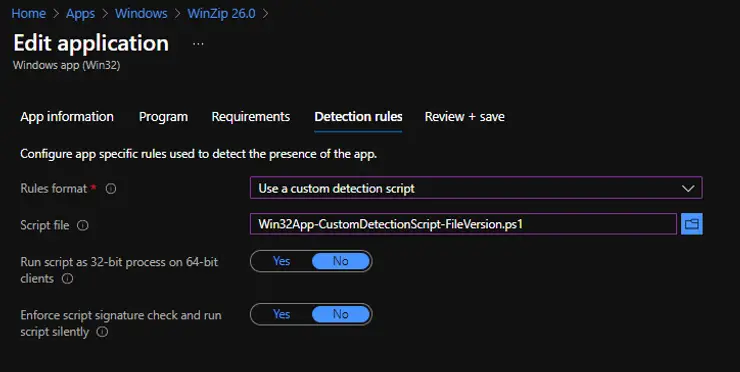
Use a custom detection Rule
PowerShell‑based detection rules are supported in Microsoft Intune to verify the presence of a Win32 application. This method allows administrators to run a custom script that defines the detection logic. To configure this option, the following details are required:
When configuring a PowerShell‑based detection rule in Microsoft Intune, the following options must be defined:
- Script file – Select a PowerShell Win32 App Detection Script that will detect the presence of the application on the client. The app is considered detected when the script returns an exit code of 0 and writes a string value to STDOUT.
- Run the script as a 32‑bit process on 64‑bit clients – Choose Yes to run the script in a 32‑bit process on 64‑bit devices. Select No (default) to run the script in a 64‑bit process. On 32‑bit clients, the script always runs in a 32‑bit process.
- Enforce script signature check – Select Yes to verify that the script is signed by a trusted publisher. This allows the script to run without warnings or prompts. Select No (default) to run the script without signature verification, which may require user confirmation.
The Intune agent evaluates the results returned by the Intune Win32 app detection script. It reads the values written to the STDOUT stream, the standard error (STDERR) stream, and the exit code.
- If the script exits with a non‑zero value, the detection fails and the application status is reported as not installed.
- If the script exits with a zero value and STDOUT contains data, the detection succeeds, and the application status is reported as installed
Exit Code and STDOUT stream
| Exit Code | STDOUT Stream | Detection State |
| 0 | Not Empty | Detected, Application installed |
| 0 | Empty | Not detected, Application not installed |
| Non zero | Empty | Not detected, Application not installed |
| Non zero | Not Empty | Not detected, Application not installed |
Source: https://www.petervanderwoude.nl/post/working-with-custom-detection-rules-for-win32-apps/
Sample Intune Win32 app detection script:
Below is a sample PowerShell Intune Win32 app detection script that can be used with the Custom Detection Rule for Win32 apps in Microsoft Intune. This script validates both file existence and file version, making it suitable for scenarios where precise Intune detection rules are required to ensure accurate application deployment and compliance.
- If the conditions match, the script returns an exit code of 0 and writes a string value to STDOUT.
- If the conditions do not match, the script still returns an exit code of 0, but without writing any value to STDOUT.
The Intune Management Extension captures the output written to STDOUT (via Write-Host) and records it in the log file.
$AppName = "Winzip ver 26.0"
$File = "D:\Program Files\WinZip26\winzip64.exe"
$FileVersion = "50.260.14610 (64-bit)"
Write-Host "Custom script based detection : $AppName"
if (Test-path $File) {
$ActualVersion = (Get-ItemProperty -Path $File).VersionInfo.FileVersion
If ($ActualVersion -eq $FileVersion) {
Write-host "Actual version: $Actualversion, Compared version: $FileVersion"
Write-host "Same version of application installed"
Exit 0}
else {
Write-host "Actual version: $Actualversion, Compared version: $FileVersion"
Write-host "Different Version of application installed"
Exit 0}
}
else {
Write-Host "File $file not found. Application not installed"
Exit 1
}
Client-side activities:
Below are excerpts from the Intune Management Extension log. In these entries, the client downloaded the deployment policy, which contains all configuration details for Intune Win32 app detection rules. The policy also includes the PowerShell detection script, stored in encrypted form. (For readability, some lines have been removed.)
In this example, DetectionType 3 represents a custom script‑based detection rule.
<![LOG[Get policies = [{"Id":"4c153c53-913e-4a75-92b1-27e53ca03876","Name":"WinZip 26.0","Version":1,"Intent":3,"TargetType":2,"AppApplicabilityStateDueToAssginmentFilters":null,"AssignmentFilterIds":null,"DetectionRule":"[{\"DetectionType\":3,\"DetectionText\":\"{\\\"EnforceSignatureCheck\\\":0,\\\"RunAs32Bit\\\":0,\\\"ScriptBody\\\":\\\"77u/JEFwcE5hbWUgPSAiV2luemlwIHZlciAyNi4wIgokRmlsZSA9ICJEOlxQcm9ncmFtIEZpbGVzXFdpblppcDI2XHdpbnppcDY0LmV4ZSIKJEZpbGVWZXJzaW9uID0gIjUwLjI2MC4xNDYxM2UgeyAKV3JpdGUtSG9zdCAiRmlsZSAkZmlsZSBub3QgZm91bmQuIEFwcGxpY2F0aW9uIG5vdCBpbnN0YWxsZWQiCkV4aXQgMAp9\\\"}\"}]","InstallCommandLine":"msiexec /i winzip260-64.msi /qn INSTALLDIR=\"D:\\Program Files\\WinZip26\"", ........
The excerpts below show the evaluation of the custom detection script.
<![LOG[[Win32App] ===Step=== Detection rules]LOG]!><time="19:10:44.5585753" date="3-1-202x2" component="IntuneManagementExtension" context="" type="1" thread="28" file=""> <![LOG[[Win32App] ProcessDetectionRules starts]LOG]!><time="19:10:44.5585753" date="3-1-2022" component="IntuneManagementExtension" context="" type="1" thread="28" file=""> <![LOG[[Win32App] ProcessDetectionRules Parsing InstallEx...]LOG]!><time="19:10:44.5585753" date="3-1-2022" component="IntuneManagementExtension" context="" type="1" thread="28" file=""> <![LOG[[Win32App] DetectionType 3]LOG]!><time="19:10:44.5595744" date="3-1-2022" component="IntuneManagementExtension" context="" type="1" thread="28" file=""> <![LOG[[Win32App] Start detectionManager SideCarScriptDetectionManager]LOG]!><time="19:10:44.5747007" date="3-1-2022" component="IntuneManagementExtension" context="" type="1" thread="28" file=""> <![LOG[[Win32App] Detection script file C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1 is saved.]LOG]!><time="19:10:44.7470933" date="3-1-2022" component="IntuneManagementExtension" context="" type="1" thread="28" file=""> <![LOG["C:\Program Files (x86)\Microsoft Intune Management Extension\agentexecutor.exe" -powershellDetection "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1" "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1quotedResultFilePath.txt" "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1quotedErrorFilePath.txt" "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1quotedTimeoutFilePath.txt" 3600 "C:\Windows\System32\WindowsPowerShell\v1.0" 0 "C:\Program Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\4c153c53-913e-4a75-92b1-27e53ca03876_1.ps1quotedExitCodeFilePath.txt" False]LOG]!><time="19:10:44.8749422" date="3-1-2022" component="IntuneManagementExtension" context="" type="1" thread="28" file=""> <![LOG[[Win32App] SideCarScriptDetectionManager Launch powershell executor in machine session]LOG]!><time="19:10:44.8779350" date="3-1-2022" component="IntuneManagementExtension" context="" type="1" thread="28" file=""> <![LOG[[Win32App] Checked Powershell script result: Custom script based detection : Winzip ver 26.0 Actual version: 50.260.14610 (64-bit), Compared version: 50.260.14610 (64-bit) Same version of application installed ]LOG]!><time="19:10:48.3363923" date="3-1-2022" component="IntuneManagementExtension" context="" type="1" thread="28" file=""> <![LOG[[Win32App] Checked Powershell script exitCode: 1 EnforceSignatureCheck: 0 RunAs32Bit: 0 InstallExRunAs: 1, result of applicationDetected: False]LOG]!><time="19:10:48.3376679" date="3-1-2022" component="IntuneManagementExtension" context="" type="1" thread="28" file="">
If any of the above Win32 app detection rules are misconfigured, the application may be offered to the client even if it is already installed. In such cases, the Intune agent cannot properly detect the application after installation, and the deployment will fail with the error code 0x87D1041C.
Conclusion
Understanding how Win32 app detection rules in Microsoft Intune work is critical for ensuring reliable application deployments. Whether detection is based on MSI, file/folder checks, registry keys, or custom PowerShell scripts, each rule must be configured correctly to avoid false negatives and deployment failures.
The Intune Management Extension log provides detailed visibility into the detection process, helping administrators troubleshoot issues and validate rule behavior. Misconfigured rules can lead to errors such as 0x87D1041C, so careful planning and testing are essential.
By leveraging the right detection method and monitoring logs effectively, IT admins can ensure that applications are accurately identified, properly installed, and consistently managed across client devices.
Frequently Asked Questions (FAQs)
What are Win32 app detection rules in Intune?
Win32 app detection rules are methods used by Intune to verify whether an application is installed and compliant on a managed device. They ensure that deployment status is accurate and help avoid reinstallation of already present apps.
Which types of detection rules does Intune support?
Intune supports multiple detection methods, including MSI product codes, file existence checks, registry key/value checks, and custom PowerShell scripts.
When should I use MSI detection rules?
MSI detection rules are best used when deploying applications packaged as MSI installers. Intune checks the MSI product code to confirm installation.
How do file and registry detection rules work?
File detection rules verify the presence of a specific file or folder path, while registry detection rules check for a particular registry key or value to confirm app installation.
Can I use PowerShell scripts for detection?
Yes. PowerShell detection rules provide flexibility to define custom logic, making them useful for complex scenarios where MSI, file, or registry checks are insufficient.
Where can I find logs for troubleshooting detection rules?
Detection rule results are logged in the Intune Management Extension (IME) logs, located at:C:\ProgramData\Microsoft\IntuneManagementExtension\Logs\IntuneManagementExtension.log.
What happens if detection rules are misconfigured?
If detection rules are incorrect, Intune may repeatedly attempt to install the app or mark it as failed. Proper configuration ensures accurate compliance reporting and smooth deployments.
Related Posts
- Deploy Win32 App Using Intune Enterprise App Catalog
- Understanding Win32 App Detection Rules
- Understanding Win32 App Requirements Rule
- Upgrade / Replace Win32 Apps with Supersedence Relationship
- Win32 App Deployment with Dependencies
- Win32 Apps vs LOB Apps
- Win32 App Deployment failed with error code 0x80070643
- Win32 App Deployment Failed with Error 0x87D1041C
- Win32 App Deployment failed with error 0x87D300C9
- Win32 App failed with error code 0x80070653
- Deploy Google Chrome for Enterprise with Intune Win32 App
- How to Prepare Win32 App Installation source for Microsoft Intune
- SCCM Device Collection Equivalents in Microsoft Intune for App Deployment
- Deploy Microsoft SQL Server Management Studio 19.02 through Intune
- Organizing Laptop and Desktop in Intune Using Filters